Bonafeyed‘s Cy4Secure is a data protection solution that safeguards an unlimited number of data fields, tables, and records contained within databases, whether deployed on premise, in the cloud, or utilized by SaaS applications. It is fully interoperable with today’s security technologies covering detection, prevention, and transportation, and protects data even after a security data breach. Our Data-Defined Security approach natively secures data, allows full database analytic operations, and keeps queried data protected when delivered to another enterprise or security domain, placed in backups or archives, or after received on endpoint devices. Cy4Secure supports an advanced 800-bit streaming cipher, AES-256 block cipher encryption, multi-factor authentication, and password-less data cryptography without impacting user workflows. When compared to other approaches, Cy4Secure goes beyond traditional data “in-flight” or “at-rest” security technologies by protecting data “in-use” within a database or database driven SaaS CRM, ERP, Retail, Health Services, Finance, Telecom or Services applications.
The underlying problem with data protection is a general lack of awareness and understanding of how to protect the data itself, not just guard the systems holding it. Data protection regulations do not specify how to safeguard data, only that “somewhere” encryption be utilized. Transit protection only secures data “in-flight”. Data “at-rest” protection only secures where data is physically stored. Traditional security solutions try to detect and prevent unauthorized access at the edge of an enterprise, but once a cybercriminal penetrates the security perimeter, data is freely available by querying the databases. When protected by Cy4Secure, unauthorized users can only receive or pilfer encrypted data. Data remains safe even while IT applies patches and updates to fix regularly discovered exploits to the perimeter security. In the event Cy4Secure protected data is lost, stolen, abandoned, or forgotten, it remains secure and is demonetized and permanently inaccessible once the crypto keys protecting it are disabled or retired, ensuring cybercriminals or non-authorized users only obtain unintelligible encrypted data.
Cy4Secure Data Security can be seamlessly and rapidly deployed in existing environments. All modern database systems can be protected without impacting user workflows, changing existing infrastructure, and with no perceivable impact to performance. Users or external customer/clients perform password-less or multi-factor authentication to validate credentials which allow access to protected data. More importantly, each data element or field can be independently encrypted/protected. No two data elements are required to share the same key or authorization requirements. Bonafeyed delivers privacy in plain sight!
Cy4Secure is Bonafeyed’s answer to the increasing threat of data breaches. Cy4Secure‘s architecture accomplishes this feat by only encrypting/decrypting data at authorized user endpoints. Our Data-Defined Security approach continuously safeguards data as it moves across different security domains, when it lands on an application server, after delivery from a cloud-based application, and finally, when the data rests on a recipient’s endpoint device. Cy4Secure uses the following security methods:
- Bonafeyed never sees or touches any customer data
- All encrypt/decrypt operations are performed on the user’s secure endpoint device (SED)
- All authentication data is hashed using SHA-512
- Shared data is encrypted before it leaves the user’s SED
- Encryption secrets are disassociated from the protected data’s location
- Data and corresponding encryption secrets only unite on an authorized user’s SED
- Agnostic Data-Defined Architecture with all transport, network, or other security protocols
- “Airgap” technology ensures keys and credential information are inaccessible to hackers
- Minimum of 800-bit size keys are utilized for strong crypto operations
- Five 9’s Availability for authentication, and crypto management services reliability and uptime
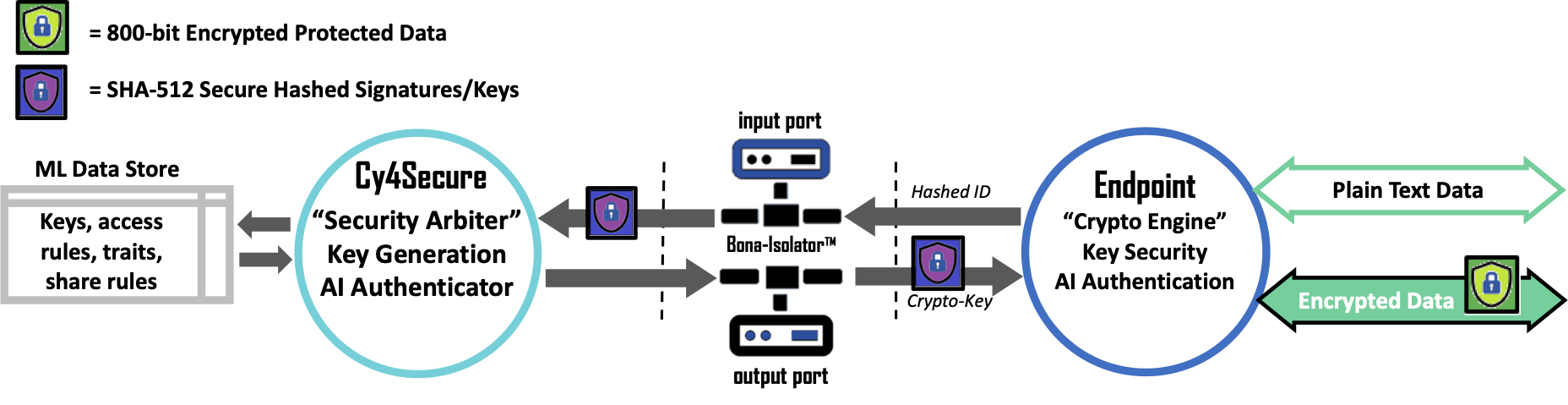
At the center of Bonafeyed’s data security is the Cy4Secure Arbiter (CSA) which is responsible for managing all crypto functions. They include maintaining crypto secrets and credentials relationship, authorizing crypto information, supporting RESTful API, enforcing encryption key lifecycles, monitoring access habits, trends, frequency to proactively detect attacks, and theft or misuse of user credentials. It stores cryptography secrets and credentials, operates in a highly reliable and available clustered and distributed configuration. The Bona-Isolator™ provides an industry leading security air gap between public facing servers and the CSA. It ensures that no direct access to the ML Data Store or the CSA is possible. The CSA is deployable within the cloud as a service or on premise using a software-defined deployment model.
The Cy4Secure SDK allows easy cryptography integration into browsers, 3rd party SaaS, and Enterprise applications for automatic deployment to endpoint devices. The SDK provides prebuilt functions to perform cryptographic operations and to interact with the CSA. It also provides an optional conversion function to make encrypted data transportable across 8-bit transport mechanisms. The SDK supports multiple languages: JavaScript, Java, C, Python, C#, and Swift.