

SaaS Use Case: Protecting Data in 3rd Party SaaS Applications
SaaS applications are cloud based solutions where the software and infrastructure are owned and managed by the application service provider. Enterprises create, access, share, and transfer data stored in the hosted application. However, when the data reaches a cloud service it resides within the SaaS application and is no longer visible to the customer’s network and requires a protection scheme that’s in-line but still allows the SaaS application to operate.
Experian released its sixth annual Data Breach Industry forecast that included its top five data breach predictions for 2019. The most susceptible breach targets are cloud vendors and wireless carriers. This places 3rd party SaaS application vendors squarely in the sights of cybercriminals.
“It's a matter of when, not if, a top cloud vendor breach will occur, compromising the sensitive information of major companies. The only question is how long it will take hackers to go to the cloud, affecting the world's largest companies and potentially billions of pieces of data.” (https://www.experian.com/blogs/ask-experian/experian-forecasts-the-top-5-data-breach-predictions-for-2019/)
Deploying Bonafeyed’s data protection technology ensures the data or data fields within a 3rd party SaaS application are encrypted and only accessible by authorized users. Even in the event of a SaaS data breach, the data remains secured and private from cyber criminals or in-network non-authorized users. Bonafeyed uses 800-bit Stream Cipher technology to stop infiltrators or prying eyes in their tracks.
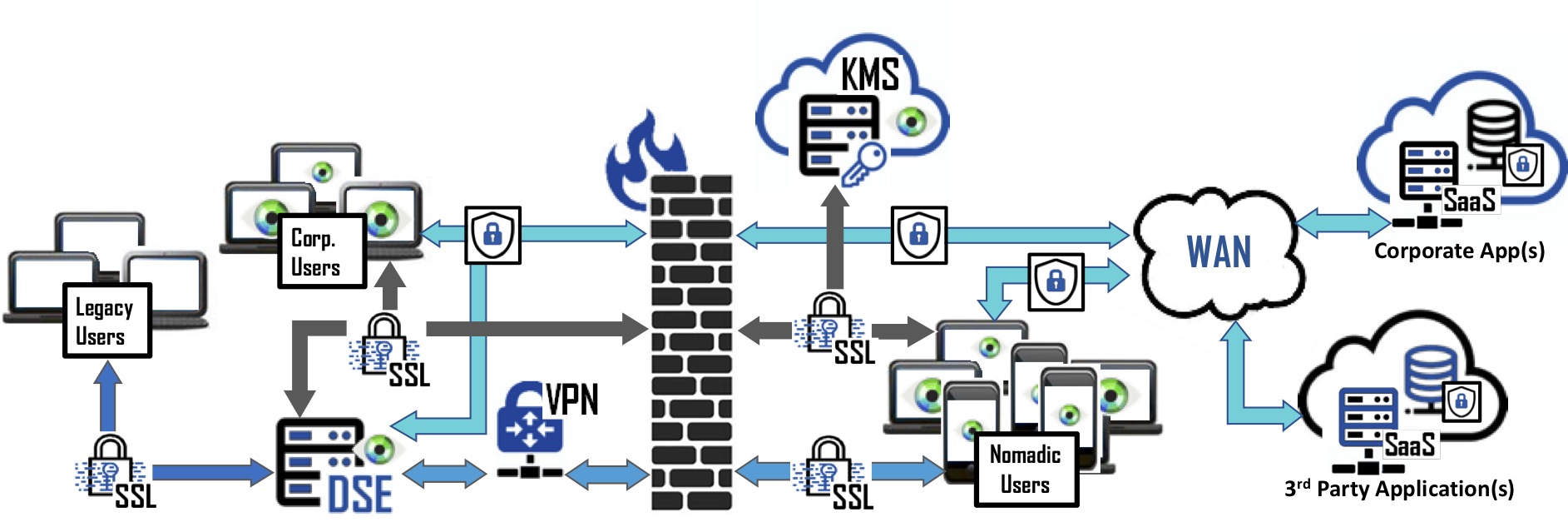
Bonafeyed’s Data Security Technology can be deployed in minutes. Enterprise IT can push browser plugins to employees’ devices or deploy Data Security Gateway, (DSE) to facilitate the fastest deployment option for legacy applications without the need for client changes. Data can be shared outside the enterprise network utilizing 2-factor authentication. Bonafeyed’s Encryption Key Management Cloud Service (KMS) validates and allows access to the protected data on the SaaS. More important is that each data field or set can be independently encrypted/protected and can be accessed by groups or single individuals. When keys are deleted or retired or encrypted data is lost, stolen, abandoned or forgotten, it remains protected and inaccessible ensuring an enterprises data in the cloud remains protected.
